FEATURED| TRENDING WITH READERS
MORE INSIGHTS

6 Ways Your Large Practice Can Begin Integrating AI Technology to Drive Efficiency
To highlight the critical results of this research, we're examining the top use cases for AI technology that physicians believe they can benefit most from.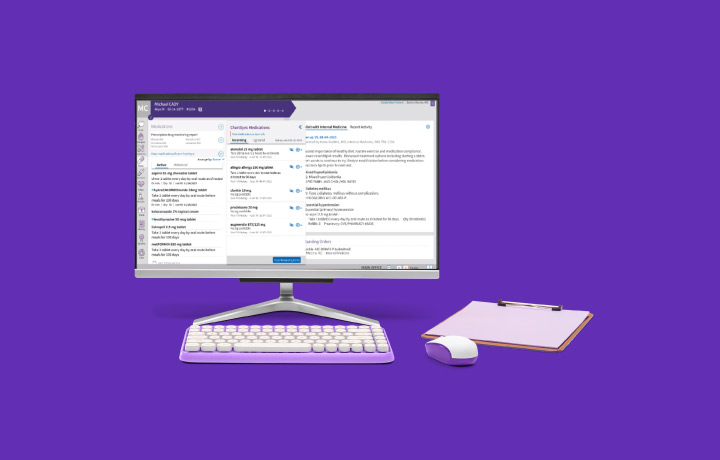
Moving Beyond Basic Data Exchange to Deliver on the Promise of Interoperability
Moving Beyond Basic Data Exchange to Deliver on the Promise of Interoperability
5 Ways the Right EHR Can Streamline Urgent Care
Increased demand for urgent care calls for top-notch EHR systems. Learn which features bring the most benefits to your organization.
Key ways your healthcare organization can use technology to simplify value-based care
Key ways your healthcare organization can use technology to simplify value-based care
Selecting the right technology for your podiatry practice
Selecting the right technology for your podiatry practice
EDITORS' PICKS

Article
What is quality in value-based care?
Article
Value-based care requires a thriving community-based healthcare ecosystem
Article
Leveraging technology to simplify value-based care – Tracking submissions and measuring performance at Oaklawn Medical Group
Article
Elevating the patient experience through data partnership
Article
Fostering accessible healthcare practices across modalities
INFOGRAPHICS
Infographic
A Quality Payment Program update
Infographic
How physicians' attitudes on the healthcare industry differ by specialty
Infographic
Breaking the burnout cycle
Infographic
5 ways to engage and support patients with chronic conditions
Infographic
The plight of the PCP
Infographic
Prior authorizations, explained
Infographic
Optimizing patient flow